-

Entrance to the Delaware Valley Intelligence Center in South Philadelphia. Photo: Dustin Slaughter
- By Dustin Slaughter, Joanne Michele, and Kenneth Lipp
CACI International, a top-tier contractor for the Department of Defense and Department of Homeland Security, and also implicated in the widely publicized accounts of detainee abuse at Abu Ghraib prison in Iraq, is now a key player in the operation of Philadelphia’s new 40,000 square foot fusion center, the Delaware Valley Intelligence Center (DVIC). Its full operational status was publicly announced in March of 2013.
Timothy Shorrock, arguably one of the most knowledgeable journalists covering government security contracting and the Intelligence Community, profiled CACI at length in his book Spies for Hire: The Secret World of Outsourced Intelligence and detailed the veritable Gold-Rush in intelligence operations out-sourcing which ensued after the World Trade Center’s collapse.
Shorrock writes of CACI:
CACI International Inc. is one of the world’s largest private intelligence services providers and is deeply involved in classified “black” operations everywhere on the globe where U.S. military forces are active.
“The best way to describe CACI is as a private supplier of signals intelligence, human intelligence, imagery, and black ops, all rolled into one enterprise,” he adds. “CACI’s intelligence contracts now make up 35 percent of the company’s revenues, 95 percent of which is earned from the federal government,” writes Shorrock. CACI boasted of $2.3 billion in revenue in 2011.
While The Declaration cannot confirm CACI’s full relationship with the DVIC’s chief, Philadelphia Police Department Inspector Walter Smith (because the center’s project manager, Christopher Bonin – a CACI employee – did not return our phone call), the company’s publicized modus operandi dealing in “analysis, collection, user outcomes, and management” suggests that Bonin may have more of a role than just getting the Center up and running. SOSSEC, an Army initiative launched after September 11th, 2001, lists on their website many participants (including another military contracting leviathan, Booz Allen Hamilton), however all documents available regarding the facility and operations place CACI as the key player.
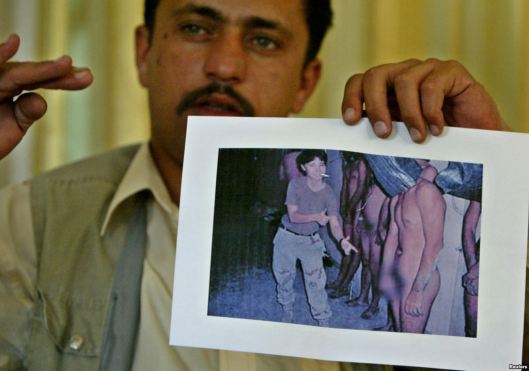
- A former prisoner at Abu Ghraib shows a photograph, now infamous, of abuse at the prison. Photo via Reuters
The Delaware Valley Intelligence Center, which Dustin Slaughter reported on in The Declaration earlier this year, is an “all crimes” model information aggregation, analysis, and distribution facility made available to law enforcement and private sector entities in a four state region, at various levels of contribution and access. It utilizes the resources of federal, state, and local authorities as well as of financial institutions, utility and telecommunication companies, providers of transit and health services, and other privately-held participants whose security and function are deemed critical to public safety and official operations.
The process ‘fuses’ these networked investigative and analytic contributions and generates a synthesized “intelligence product” – an ever more ubiquitous offering most often in the form of a text-based ‘digest’ of current events in the threat register (see the DHS Open Source Critical Infrastructure Report for a watered-down example), but more and more frequently being advertised as featuring highly-interactive, user-friendly graphical interfaces linked to stations and cameras reporting incidents in real time.
CACI’s involvement in the DVIC is under the auspices of The System of Systems Security Consortium, SOSSEC. SOSSEC purports to provide yet another solution to “events of 9/11” which “spawned a U.S. Army initiative to ‘Provide Solutions to meet Local, Regional and National Force Protection (FP), Homeland Defense (HD), and Homeland Security (HS) needs with a System of Systems Scalable, Interoperable and Integrated Approach for Addressing Emerging 21st Century Threats” (DVIC Brochure). The Consortium’s flagship project seems to be the Philadelphia fusion center, and further, as their website as much as explains, federal involvement is largely a function of and vehicle for contract development by defense giant CACI (Ever Vigilant).
On the Spies for Hire site Shorrock further details CACI’s contracting profile. Their current single biggest contract is with the US Army, $450 million dollars to provide multi-front, technology-intensive domain awareness and command capabilities, a field known as C4ISR ( for command, control, communications, computers, intelligence, surveillance and reconnaissance) within the military.
“Other customers include the U.S. Navy’s littoral and mine warfare program, the Air Force’s Pacific Command and Control unit, and the Defense Information Systems Agency (DISA), the Pentagon unit responsible for network centric warfare. Elsewhere in the Intelligence Community (IC), CACI holds major contracts with the Department of Homeland Security and the DHS’s U.S. Customs and Border Protection agency.”
But the contract that CACI will always be known for is the one to provide interrogators at Abu Ghraib.
CACI nor any other private company has faced any legal or civil penalties for the serious mistreatment of prisoners at the Iraqi prison, prisoners for whom it was responsible under its contract with the US military. Some members of the military did face courts martial, non-judicial punishments, and administrative reprimands, but those responsible for designing and implementing the policies that created the culture of corruption and recklessness that came to a public head in the Abu Ghraib prison scandal remain in their positions: awarding or receiving huge sums of taxpayer money to perform duties of similar scope and gravity.
The 21st Century Fusion Center is a massive and unwieldy dynamo even with the support of the most able and earnest of engineers. The sheer volume of data being collected, “networked,” and analyzed defies exhaustive sifting, and yet is used to produce, often on demand, “intelligence” of a frequently though not surprisingly dubious quality.
Worse, when such operations are manned by inept or less-than-scrupulous agencies, they can pose a serious risk of targeting innocent people and chilling civil liberties with arbitrary engagements, without providing near the tide-turning payoff in terrorism prevention that such a deep-pocketed surrender of personal liberty and privacy one would expect to purchase.
A 2011 article in the Hastings Law Journal, “Networked Accountability for the Domestic Intelligence Apparatus,”* cites multiple cases where law enforcement working in concert with fusion center operations, especially when attempting to presage indicators of potential terrorist activity, have far overreached their investigative capability and license and infringed on lawful activities. One such circumstance:
“Over a nineteen-month period in 2004 and 2005, Maryland state police conducted surveillance of human rights groups, peace activists, and death penalty opponents. As a result, fifty-three nonviolent political activists were classified as “terrorists,” including two Catholic nuns and a Democratic candidate for local office.
A Maryland fusion center shared the erroneous terrorist classifications with federal drug enforcement and terrorist databases, as well as with the National Security Administration (NSA).
Even more grim, as the article explains, is the fact that the networked complexity of domestic intelligence operations allows it and its separate participants virtual indemnity when their actions are harmful, and the system remains an accountability vacuum. The article’s authors further clarify the potential for fusion centers to manipulate information to tailor to the interests of their stakeholders, the very agencies and corporations who depend upon a perceived need for surveillance and continued burgeoning of our national security regime to to generate huge profits.
“The [Fusion Center intelligence sharing environment] has yet to provide a systematic redress mechanism to remove misinformation from databases spread throughout the networked environment or to address the stigma that can result from misclassifications. Had the ACLU of Maryland not fortuitously discovered the fusion center’s activities in connection with an open records request, the political activists might have remained on these watch lists. In response to these and other similar incidents, Bruce Fein, an associate deputy attorney general under Ronald Reagan, argued that fusion centers conceive the business of gathering and sharing intelligence as ‘synonymous with monitoring and disparaging political dissent and association protected by the First Amendment.’ [emphasis added]”
The article notes that this assessment was confirmed by a fusion center official, who commented:
You can make an easy kind of a link that, if you have a protest group protesting a war where the cause that’s being fought against is international terrorism, you might have terrorism at that protest. You can almost argue that a protest against [the war] is a terrorist act.
Taking into account CACI’s history of alleged abuses, the Center’s existence becomes even more problematic when the oft-criticized track record of fusion centers as being wasteful and ineffectual is taken into account, as Dustin Slaughter elucidated in his previous piece for The Declaration, The Questionable Benefits of Philadelphia’s New Fusion Center.
Slaughter explains how Philadelphia Mayor Michael Nutter, a vocal proponent of the Center, as well as law enforcement officials, appear to be ignoring a stark reality now plaguing the growth of these often lauded but clearly under-performing fusion centers: They are an enormous waste of taxpayer money.
Since September 11th, 2001, the cost for construction of fusion centers and their operations have totaled $1.4 billion.
A Senate report (in full available here and a summary here) issued on October 3rd, 2012 “could identify no reporting which uncovered a terrorist threat, nor could it identify a contribution such fusion center reporting made to disrupt an active terrorist plot.”
Republican Senator and U. S. Senate Permanent Subcommittee on Investigations chairperson Tom Coburn blasted fusion center performance, stating:
It’s troubling that the very ‘fusion’ centers that were designed to share information in a post-9/11 world have become part of the problem. Instead of strengthening our counterterrorism efforts, they have too often wasted money and stepped on Americans’ civil liberties.
Harold “Skip” Vandover, a former director at the Department of Homeland Security’s reporting branch, is quoted in the report with regards to the actionable “intelligence” being fed to analysts at fusion centers:
There were times when it was, ‘What a bunch of crap is coming through.’
Questions about the real focus of fusion center intelligence gathering and analyzing must be asked, especially in light of recent revelations that centers were actively collecting information (with the help of the FBI and private sector entities such as the Federal Reserve and Wall Street banks) on the Occupy Wall Street Movement, which counter-terrorism officials considered a domestic terror threat despite its clear use of non-violent tactics. What has also become known through a Freedom of Information Act (FOIA) request by the Partnership for Civil Justice fund is that the FBI may very well have been aware of sniper plots to assassinate Occupy organizers in Houston, Texas and Gainesville, Florida, but did not alert activists to this threat.

- With revelations mounting in the press about US agencies’ policies of “hard questioning” interrogation techniques and, explicitly, torture in the name of a security which can clearly not be provided by such derogating “enhancements,” would the citizens of Philadelphia truly be comforted to know that they are being guarded with the assistance of a corporation like CACI, whose history is marred by wrongdoing and under a protective system seemingly designed to prevent the correcting of wrongs?
Sleep tight, City of Brotherly Love.
* Network Accountability for the Domestic Intelligence Apparatus. Danielle Keats Citron, University of Maryland Francis King Carey School of Law; Yale University – Yale Information Society Project; Stanford Law School Center for Internet and Society. Frank A. Pasquale III, Seton Hall University – School of Law; Yale University – Yale Information Society Project. 2011 Hastings Law Journal, Vol. 62, p. 1441, 2011. U of Maryland Legal Studies Research Paper No. 2010-48
[…] C. Philly Declaration (4/17): Military Contracting Giant Implicated in Iraq Prisoner Abuse Plays Major Role in Philly’s New Fusi… […]
LikeLike
[…] di persone, molte delle quali non lavorano neppure alle dipendenze del governo americano, ma di Contractor esterni, compagnie che hanno già dimostrato non avere scrupoli nemmeno a fornire e a tollerare […]
LikeLike
[…] di persone, molte delle quali non lavorano neppure alle dipendenze del governo americano, ma di Contractor esterni, compagnie che hanno già dimostrato non avere scrupoli nemmeno a fornire e a tollerare […]
LikeLike
[…] Military Contracting Giant Implicated in Iraq Prisoner Abuse Plays Major Role in Philly’s New Fusi… […]
LikeLike
Excellent piece, thanks for this. I had no idea this existed before reading this article.
LikeLike
Thank you; it seems a novelty to most, though the City has touted the center highly.
LikeLike
Your style is very unique in comparison to other people I have read stuff from. Thanks for posting when you’ve got the opportunity, Guess I will just book mark this web site.|
LikeLike
[…] fundamentals to ensure academic success, including overcrowded and unsafe public schools, all while odious “national security” contractors line their pockets and poorer neighborhoods bear the brunt of police repression, thanks in part to intense […]
LikeLike